Example 2: Malicious Activity
Sometimes the goal of a cyber attack is not to slow down or make a website unavailable, but to compromise it. Such attacks include SQL and command injections, Cross-Site Scripting, Cross-Site Request Forgery, Path / Directory Traversal, File Inclusion, as well as known vulnerability exploits and vulnerability scanning.
These attacks target the web application, rather than the server, so they are handled at L7 by the WAF (Web Application Firewall).
Identifying the Attack
Attacks aiming to compromise websites tend to target dynamic pages and endpoints (login pages, search, and forms), authentication-related resources, file-handling endpoints, and other sensitive paths, such as /admin, /config, and similar.
Spikes of activity targeting potentially sensitive URLs are signs of such an attack. Logs will also often show errors, as attackers are probing for targets.
Example
Let us examine a specific log file for the (www.)bank.cz domain, specifically the Top 10 URLs.
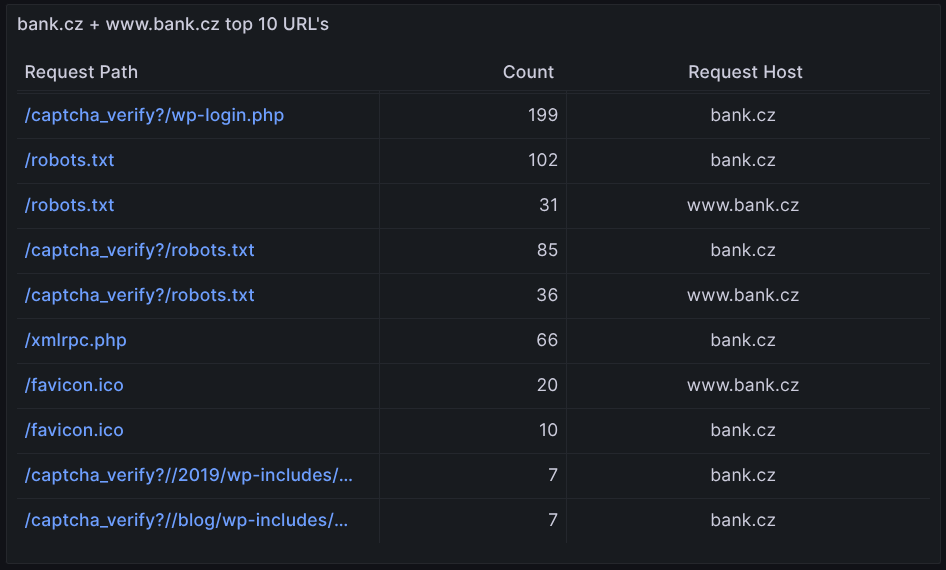
We notice frequent attempts to access /captcha-verify/?wp-login.php and xmlrpc.php. These may include brute-force login attempts, likely prevented by the captcha page, as well as attempts to exploit content, core or plugin vulnerabilities.
Manual Attack Mitigation
The recommended first response is to increase the WAF paranoia level. This will enforce strict traffic checks and block any suspicious activity, returning a 456 error whenever the firewall blocks such a request.
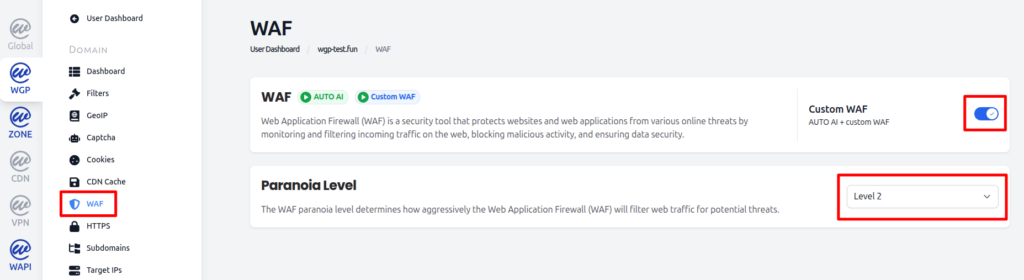
These errors should then appear in the Anomalies in Location table in Grafana. After increasing the paranoia level, monitor the anomalies in Grafana, as well as the website function and performance in general.

Resolution
If the site is running satisfactorily at the WAF paranoia level 2, consider leaving it set at that level indefinitely.
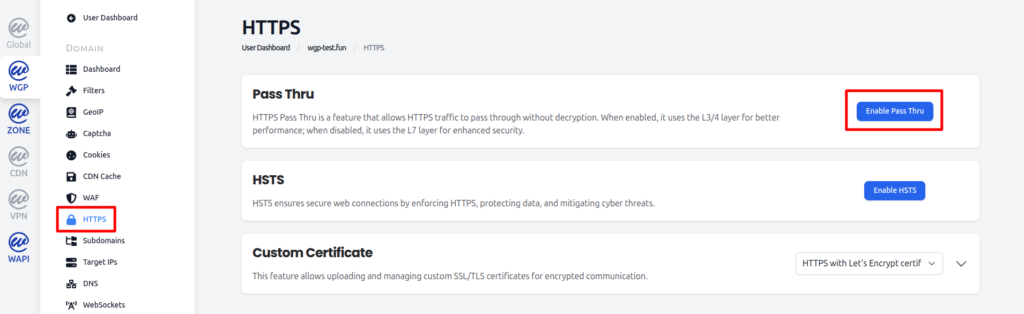
If either level of WEDOS.protection WAF causes the website to not function correctly, or if data decryption on the proxy is a security or performance concern, you can always enable HTTPS Pass Thru mode and set up your own Firewall or other security solution on your server.